Fast Quantum Byzantine Agreement: Difference between revisions
No edit summary |
No edit summary |
||
| Line 1: | Line 1: | ||
The classical problem of Byzantine agreement [[Quantum Byzantine Agreement#References|(8)]] is about reaching agreement in a network of <math>n</math> players out of which <math>t</math> players may be faulty. Each player starts with an input bit <math>b_i</math> and the goal is for all correct players to output the same bit <math>d</math> | The classical problem of Byzantine agreement [[Quantum Byzantine Agreement#References|(8)]] is about reaching agreement in a network of <math>n</math> players out of which <math>t</math> players may be faulty. Each player starts with an input bit <math>b_i</math> and the goal is for all correct players to output the same bit <math>d</math> ''agreement'', under the constraint that <math>d = b_i</math> at least for some node <math>i</math> ''validity''. The [[hardness]] of this task depends on the [[failure model]] of the faulty (sometimes called [[adversary]]) players. In Byzantine agreement, the faulty players are assumed to show the most severe form of failure known as Byzantine failures. In this model, faulty players behave arbitrarily, can collude and even act maliciously trying to prevent correct players from reaching agreement. Byzantine agreement is an important problem in classical distributed systems, used to guarantee consistency amongst distributed data structures. | ||
'''Tags:''' [[:Category: Quantum Enhanced Classical Functionality|Quantum Enhanced Classical Functionality]][[Category: Quantum Enhanced Classical Functionality]], [[:Category: Multi Party Protocols|Multi Party Protocols]] [[Category: Multi Party Protocols]], [[:Category:Specific Task|Specific Task]][[Category:Specific Task]], consensus task, failure resistant distributed computing | '''Tags:''' [[:Category: Quantum Enhanced Classical Functionality|Quantum Enhanced Classical Functionality]][[Category: Quantum Enhanced Classical Functionality]], [[:Category: Multi Party Protocols|Multi Party Protocols]] [[Category: Multi Party Protocols]], [[:Category:Specific Task|Specific Task]][[Category:Specific Task]], consensus task, failure resistant distributed computing | ||
Revision as of 04:53, 18 April 2019
The classical problem of Byzantine agreement (8) is about reaching agreement in a network of Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle n} players out of which Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle t} players may be faulty. Each player starts with an input bit Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle b_i} and the goal is for all correct players to output the same bit agreement, under the constraint that Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle d = b_i} at least for some node validity. The hardness of this task depends on the failure model of the faulty (sometimes called adversary) players. In Byzantine agreement, the faulty players are assumed to show the most severe form of failure known as Byzantine failures. In this model, faulty players behave arbitrarily, can collude and even act maliciously trying to prevent correct players from reaching agreement. Byzantine agreement is an important problem in classical distributed systems, used to guarantee consistency amongst distributed data structures.
Tags: Quantum Enhanced Classical Functionality, Multi Party Protocols, Specific Task, consensus task, failure resistant distributed computing
Assumptions
- We assume that the original input qubit is unknown and the protocol is independent of the original input state (universality).
- The output copies are not identical and we are able to control the likelihood (fidelity) of the output copies to the original state by pre-preparing the ancillary states with special coefficients.
Outline
In this protocol, there are three main stages. The first stage is a preparation stage. we prepare two ancillary states with special coefficients which will lead to the desired flow of the information between copied states. The original state will not be engaged at this stage. At the second stage the cloner circuit will act on all the three states (the original and two other states) and at the second stage the two copied state will appear at two of the outputs and one of the outputs should be discarded. The Procedure will be as following:
- Prepare two blank states and then perform a transformation taking these two states to a new state with pre-selected coefficients in such a way that the information distribution between two final states will be the desired.
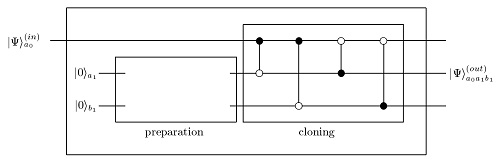 Graphical representation of the network for the asymmetric cloner. The CNOT gates are shown in the cloner section with control qubit (denoted as ) and a target qubit (denoted as Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle \circ} ). We separate the preparation of the quantum copier from the cloning process itself.
Graphical representation of the network for the asymmetric cloner. The CNOT gates are shown in the cloner section with control qubit (denoted as ) and a target qubit (denoted as Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle \circ} ). We separate the preparation of the quantum copier from the cloning process itself. - Perform the cloner circuit. the cloner circuit consists of four CNOT gate acting in all the three input qubits. For every CNOT gate, we have a control qubit (which indicates whether or not the CNOT should act) and a target qubit (which is the qubit that CNOT gate acts on it and flips it).
- The two asymmetric clones will appear at two of the outputs (depending on the preparation stage) and the other output should be discarded.
Notations Used
- The original input state
- The density matrix of the input pure state equal to
- The scaling parameter of the first clone
- The scaling parameter of the second clone
- The output density matrix of the first clone (equal to if the output state is pure)
- The output density matrix of the second clone (equal to if the output state is pure)
- The ``Identity" or completely mixed density matrix
- state of the ancillary qubits before preparation phase
- Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle |\psi\rangle_{m_1,n_1}:} state of the ancillary qubits after the preparation
- amplitudes (or coefficients) of the prepared state $|\psi\rangle_{m_1,n_1}$. These coefficients are being used to control the flow of the information between the copies before starting the cloning process.
- Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle P_{k,l}:} The CNOT gate where the control qubit is Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle k} and the target qubit is Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle l}
- Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle |\psi\rangle_{out}:} The total output of the asymmetric cloning circuit
- Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle |\Phi^+\rangle = \frac{1}{\sqrt{2}}(|00\rangle + |11\rangle):} Bell state
- Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle |+\rangle = \frac{1}{\sqrt{2}}(|0\rangle + |1\rangle):} Plus state. The eigenvector of Pauli X
Properties
- The protocol assumes that the original input qubit is unknown and the protocol is independent of the original input state (universality).
- The output copies are not identical and we are able to control the likelihood (fidelity) of the output copies to the original state by pre-preparing the ancillary states with special coefficients.
- Claims for General case:
- Following inequality holds between the scaling factors Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle s_0}
and Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle s_1}
- Following inequality holds between the scaling factors Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle s_0}
and Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle s_1}
Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle s_0^2 + s_1^2 + s_0 s_1 - s_0 - s_1 \leq 0}
- This elliptic inequality shows the possible value of the scaling parameters.
- Trade-off inequality between the fidelities of the clones:
Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle \sqrt{(1 - F_a)(1 - F_b)} \geq \frac{1}{2} - (1 - F_a) - (1 - F_b)}
- Optimality is provided when the fidelities of two clones, Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle F_a} and Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle F_b} , saturate the above inequality
- Claims for Special case with bell state:
- Following ellipse equation holds between the scaling factors Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle a}
and Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle b}
- Following ellipse equation holds between the scaling factors Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle a}
and Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle b}
Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle a^2 + b^2 + ab = 1}
- Following equations holds for fidelities of the clones:
Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle F_a = 1 - \frac{b^2}{2}, F_b = 1 - \frac{a^2}{2}}
Pseudo Code
General Case
For more generality, we use the density matrix representation of the states which includes mixed states as well as pure states. For a simple pure state Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle |\psi\rangle}
the density matrix representation will be Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle \rho_{\psi} = |\psi\rangle\langle\psi|}
. Let us assume the initial qubit to be in an unknown state Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle \rho_{\psi}}
. Our task is to clone this qubit universally, i.e. input-state independently, in such a way, that we can control the scaling of the original and the clone at the output. In other words, we look for output which can be represented as below:
Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle \rho_{a}^{out} = s_0 \rho_{\psi} + \frac{1 - s_0}{2} \hat{I}}
Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle \rho_{b}^{out} = s_1 \rho_{\psi} + \frac{1 - s_1}{2} \hat{I}}
Here we assume that the original qubit after the cloning is “scaled” by the factor Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle s_0}
, while the copy is scaled by the factor Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle s_1}
. These two scaling parameters are not independent and they are related by a specific inequality.
Stage 1 Cloner State Preparation
- Prepare the original qubit and two additional blank qubits Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle m} and Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle n} in pure states: Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle |0\rangle_{m_0} \otimes |0\rangle_{n_0} \equiv |00\rangle}
- Prepare Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle |\psi\rangle_{m_1,n_1} = c_1|00\rangle + c_2|01\rangle + c_3|10\rangle + c_4|11\rangle}
, where the complex Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle c_i}
coefficients will be specified so that the flow of information between the clones will be as desired.
At this stage the original qubit is not involved, but this preparation stage will affect the fidelity of the clones at the end of the process. - To prepare the Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle |\psi\rangle_{m_1,n_1}} state, a Unitary gate must be performed so that:
Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle U|00\rangle = |\psi\rangle_{m_1,n_1}}
- Use following relations to specify Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle c_j}
in terms of Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle a}
and Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle b}
:
Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle c_1 = \sqrt{\frac{s_0 + s_1}{2}}}
, Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle c_2 = \sqrt{\frac{1 - s_0}{2}}}
, Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle c_3 = 0}
, Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle c_4 = \sqrt{\frac{1 - s_1}{2}}}
these Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle c_j}
satisfy the scaling equations and also the normalization condition of the state Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle |\psi\rangle_{m_1,n_1}}
. They are being used to control the flow of information between the clones
Stage 2 Cloning Circuit
- The cloning circuit consists of four CNOT gates acting on original and pre-prepared qubits from stage 2. We call the original qubit Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle |\psi\rangle_{in}} , ``first qubit", the first ancillary qubit of Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle |\psi\rangle_{m_1,n_1}} , ``second qubit" and the second one, ``third qubit". The CNOT gates will act as follows:
- First CNOT acts on first and second qubit while the first qubit is control and the second qubit is the target.
- Second CNOT acts on first and third qubit while the first qubit is control and the third qubit is the target.
- Third CNOT acts on first and second qubit while the second qubit is control and the first qubit is the target.
- Forth CNOT acts on first and third qubit while the third qubit is control and the first qubit is the target.
- Mathematically the cloning part of the protocol can be shown as:
Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle |\psi\rangle_{out} = P_{3,1} P_{2,1} P_{1,3} P_{1,2} |\psi\rangle_{in} |\psi\rangle_{m_1,n_1}}
Stage 3 Discarding ancillary state
- Discard one of the extra states. The output states will be the first and second (or third) output.
Special case with bell state:
Stage 1 Cloner state preparation
- Prepare the original qubit and two additional blank qubits Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle m} and Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle n} in pure states: Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle |0\rangle_{m_0} \otimes |0\rangle_{n_0} \equiv |00\rangle}
- Prepare Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle |\psi\rangle_{m_1,n_1} = a|\Phi^{+}\rangle_{m_1,n_1} + b|0\rangle_{m_1} |+\rangle_{n_1}}
, where Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle |\Phi^{+}\rangle}
is a Bell state and Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle |+\rangle = \frac{1}{\sqrt{2}}(|0\rangle + |1\rangle)}
. In this case, the density matrix representation of the output states will be:
Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle \rho_{a}^{out} = (1 - b^2) |\psi\rangle\langle\psi| + \frac{b^2}{2} \hat{I}}
Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle \rho_{b}^{out} = (1 - a^2) |\psi\rangle\langle\psi| + \frac{a^2}{2} \hat{I}}
Stage 2 Cloning Circuit
- The cloning circuit is exactly the same as the general case. after the cloning circuit, the output state will be:
Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle a|\psi\rangle_{in} |\Phi^+\rangle_{m,n} + b|\psi\rangle_m |\Phi^+\rangle_{in,n}}
The reduced density matrix of two clones A and B can be written in terms of their fidelities:
Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle \rho_{a}^{out} = F_a |\psi\rangle\langle\psi| + (1 - F_a)|\psi^{\perp}\rangle\langle\psi^{\perp}|}
Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle \rho_{b}^{out} = F_b |\psi\rangle\langle\psi| + (1 - F_b)|\psi^{\perp}\rangle\langle\psi^{\perp}|}
Stage 3 Discarding ancillary state
- The same as the general case.
Further Information
- The protocol (3) is based on the classical protocol of (7), where the classical Oblivious Common Coin is replaced by a Quantum version, which is based on the Verifiable Quantum Secret Sharing Scheme presented in (4). The protocol of (7) also runs in constant expected time, but can only deal with limited-information adversaries. This means that the adversaries can not read communication between honest parties and read their internal state. The classical lower bound in the same model of Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle \Omega(\sqrt{n \log n})} is proven in (6).
- The work (3) also provides a protocol in a weaker failure model known as fail-stop failures. Here the nodes will crash and stop working indefinitely (stop responding). Another protocol in the same model is presented in (2).
- Another weakened version of the problem, known as detectable byzantine agreement, is solved with quantum resources in (5) (and following works). In detectable byzantine agreement, the protocol is also allowed to abort (upon detecting failures) instead of reaching agreement.














